A $4.1 Million Average Loss: Why AI Deepfake BEC Is the Most Underestimated Risk in Your Enterprise
Cybersecurity leaders have spent years preparing for ransomware outbreaks, advanced persistent threats, zero-day vulnerabilities, and large-scale data breaches. Security budgets, boardroom conversations, and enterprise cyber strategies have traditionally focused on attacks that disrupt systems, expose data, or generate public headlines. But one of the most financially devastating threats facing enterprises today operates very differently.
It does not encrypt files.
It does not trigger endpoint alerts.
It does not crash infrastructure.
Instead, it quietly manipulates trust, authorizes fraudulent financial transactions, and drains enterprise funds before organizations even realize an attack occurred.
Read More: https://tinyurl.com/ydw8f9th
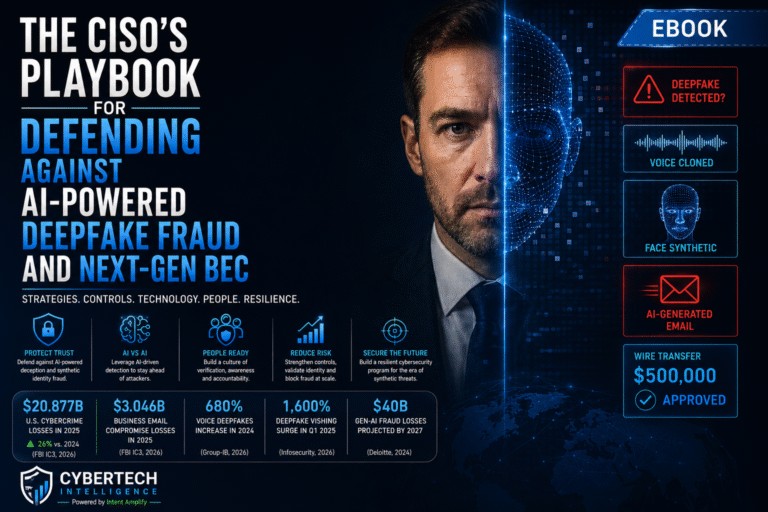
AI-powered deepfake Business Email Compromise (BEC) has rapidly evolved into one of the most underestimated risks in enterprise cybersecurity, and the financial consequences are escalating at a pace most organizations are still unprepared for.
The numbers alone should immediately force security leaders to rethink how they approach fraud prevention and operational risk. Average losses from AI-augmented BEC attacks have now crossed $4.1 million per incident, dramatically exceeding the impact of traditional phishing campaigns. This is no longer an isolated threat affecting a handful of global enterprises. AI-enhanced BEC attacks are becoming operationally scalable, financially devastating, and increasingly accessible to cybercriminals with minimal technical expertise.
Modern deepfake BEC attacks are fundamentally different from traditional email fraud. Attackers no longer rely on poorly written phishing emails filled with grammatical mistakes and suspicious requests. Generative AI has completely transformed the sophistication level of enterprise impersonation attacks.
Today’s attackers can scrape executive audio from earnings calls, conference appearances, webinars, LinkedIn videos, or publicly available interviews. With only seconds of recorded audio, AI-powered voice cloning tools can generate highly convincing synthetic replicas of executives, finance leaders, or senior management personnel. At the same time, large language models can craft perfectly written emails that mirror internal communication styles, executive tone, and organizational vocabulary with alarming precision.
The result is an attack chain specifically engineered to bypass both human skepticism and traditional detection mechanisms.
A finance executive receives what appears to be a legitimate request from the CFO regarding an urgent wire transfer. Minutes later, a confirmation call arrives using a synthetic voice clone that sounds identical to the executive they trust. The language is professional. The urgency feels authentic. The context appears legitimate. Traditional red flags simply no longer exist.
This is exactly why AI deepfake BEC is so dangerous. The attack is designed not to break systems, but to manipulate decision-making itself.
The biggest challenge organizations face today is that most enterprise defenses were never built for this type of threat. Security awareness training historically focused on detecting suspicious emails, identifying malicious attachments, and recognizing social engineering patterns that humans could visibly identify. AI-generated impersonation attacks change the equation completely because the content itself often appears flawless.
Research increasingly shows that human detection capabilities are collapsing against high-quality synthetic media. Employees are not failing because they are careless or poorly trained. They are failing because modern deepfake technologies are specifically optimized to imitate trust signals at a level most humans cannot reliably distinguish from reality.
This creates a major strategic problem for CISOs and enterprise security teams. Organizations can no longer depend solely on employees identifying suspicious behavior through intuition or visual cues. Verification processes themselves must evolve.
One of the most important lessons emerging from recent AI-driven fraud incidents is that procedural controls are becoming more valuable than content detection alone. Enterprises must redesign critical financial workflows around the assumption that any email, phone call, or video interaction could potentially be synthetic.
That means eliminating single-channel authorization for high-value transactions. It means requiring mandatory out-of-band verification using independently validated communication channels. It means implementing approval delays for vendor banking changes and creating operational friction that prevents urgency-driven financial actions.
The organizations adapting fastest to this new reality are focusing less on trying to “spot the fake” and more on making fraudulent requests operationally impossible to execute without layered validation.
Another reason AI deepfake BEC remains underestimated is because the true scale of financial loss is likely far larger than public reporting suggests. Many organizations avoid disclosing fraud incidents due to reputational concerns, regulatory sensitivity, shareholder pressure, or internal embarrassment. As a result, public loss statistics may only represent a fraction of the actual damage occurring across global enterprises.
This hidden exposure makes AI-enhanced BEC particularly dangerous from a governance and board-level risk perspective. Security leaders may already be significantly underestimating their organization’s actual exposure window.
At the same time, attackers are becoming faster, cheaper, and more automated. Generative AI tools continue lowering the barrier to entry for cybercriminal operations. Threat actors no longer require advanced social engineering expertise to conduct convincing impersonation campaigns. AI systems can now automate much of the attack preparation process, from message creation to voice generation and contextual targeting.
For enterprises, this means the attack surface is expanding rapidly while the cost of launching sophisticated fraud operations continues shrinking.
The cybersecurity conversation around AI has largely focused on productivity, automation, and innovation. But AI’s impact on cybercrime may ultimately prove even more disruptive. Deepfake-enabled fraud attacks are exposing a fundamental weakness inside modern enterprises: the assumption that communication itself can still be trusted.
That assumption is disappearing.
Security leaders now face a new operational reality where voices can be cloned, video identities can be fabricated, and written communications can be generated with near-perfect contextual accuracy. Defending against that environment requires far more than upgraded detection software. It requires redesigning enterprise trust models from the ground up.
Organizations that continue treating AI-powered BEC as a niche fraud category or an extension of traditional phishing risk making a dangerous strategic mistake. This is not simply a more advanced phishing campaign. It is the industrialization of synthetic deception at enterprise scale.
The companies that respond early by strengthening financial verification processes, modernizing employee response protocols, deploying layered fraud prevention controls, and operationalizing deepfake resilience strategies will be significantly better positioned to withstand the next wave of AI-enabled cybercrime.
The ones that wait may discover the true cost of synthetic trust only after millions have already disappeared.
Read More: https://tinyurl.com/ydw8f9th